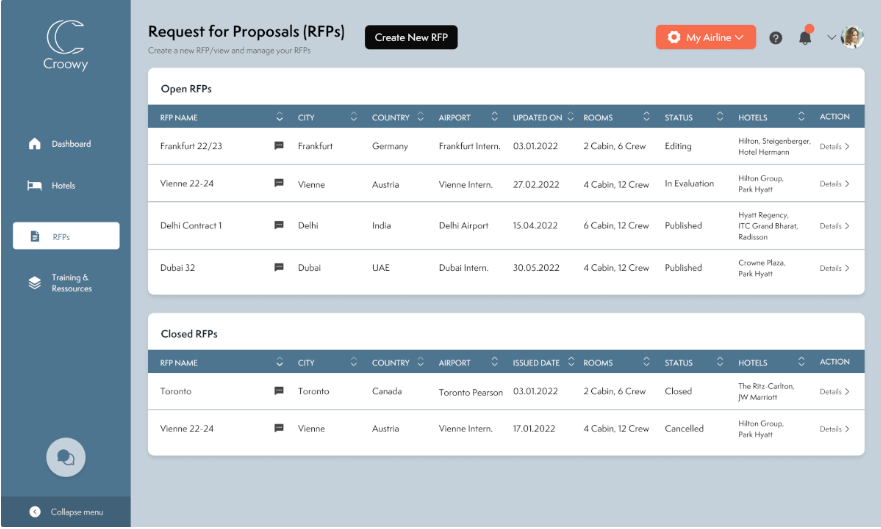
Croowy is a Software as a Service (SaaS) platform and allows Hotels as well as Airlines to get started within minutes. Our customers do not need to take care about hosting, maintenance and security updates, because our Croowy Security Experts do it for them. You can trust that we invest time and money to keep their data confidential, integer and available at all time.
But how do we actually strive to keep this promise? Below is the non-exhaustive list of our most important IT Security practices to keep our customers data secure:
Croowy Security Practices
“Security and Privacy are our highest priorities.”
Hermann Wagner, Co-Founder
We enforce the following security and privacy mechanisms to stay compliant and ensure confidentiality, integrity and availability of Croowy and our customer’s data:
- We comply with GDPR and only process data according to our privacy policy.
- Our employees and externals get a yearly Security & Privacy training.
- All data is encrypted at rest.
- All data is encrypted in transit. Over the Internet as well as internally.
- Zero Trust Security. We don’t trust the network perimeter and VPNs. All requests to our internal apps and (customer) data are individually authenticated and authorised based on the user’s credentials and context.
- Battle-tested Cloud Infrastructure. We do not own or maintain our own servers. Croowy runs on Google Cloud Platform which is certified to many different security standards like ISO27001, SOC 1/2/3, PCI DSS, FIPS 140-2, FedRamp, etc.). GCP is trusted by Enterprises like Lufthansa Group, Hilton HHonors, Amadeus, Latam Airlines, Deutsche Bank, Spotify, Apple, MediaMarktSaturn, Ikea, Renault, Vodafone, and many more. Google also implements a variety of measures to keep the infrastructure secure.
- Managed Services and automatic updates. We avoid using Infrastructure as a Service, but instead Serverless and managed Services. This ensures that our applications and data always run on compute resources which have the latest Operating system and security updates. It also allows for flexible scalability and ensures availability of our services.
- We store and process data within the European Union.
- Developers have no access to user data and user data is not used in other environments like Staging or QA.
- Developers have no access to the prod environment. Applications get deployed by the CD pipeline.
- Secrets are stored in a dedicated Secrets manager and injected by the Continuous Deployment pipeline during deployment.
- We perform static and automatic security checks of our code.
- We don’t store passwords or credit card information and also don’t implement authentication or payments. This is done through providers who are experts in this domain like Auth0 and Stripe.
- We have L3, L4 and L7 DDoS protection.
- We use a Web-application firewall with predefined OWASP Top 10 rules as well as custom rules.
- Our applications run in isolated containers. In case one container gets compromised the attacker can not escalate privileges or expand to other servers.
- Our application containers get scanned by container vulnerability scanners.
- Croowy Administrators are forced to use 2-factor authentication for access.
Our practices related to Security include more than just these 18 points like Infrastructure as Code, Backups and a high-availability infrastructure setup. In case you want a deep-dive feel free to reach out to us at admin@croowy.de